Security Policy Alerts Disabled
Risk Level- Medium
Description
The plugin ensures activity log alerts for create or update Security Policy Rule events are enabled. Monitoring for create or update Security Policy Rule events gives insight into policy changes and may reduce the time it takes to detect suspicious activity.
About the Service
Alerts: Alerts in Azure in the most simple of terms can be termed as a notification centre for all the things in Azure. Users can create, view and manage all the alert rules from a single place including metric rules, log alerts and activity log alerts. Customized alerts can be created by selecting the alert target (can be resource, subscription or anything on their azure account), the rule condition managing action groups(specifications about actions to be taken whenever an alert is triggered). To sum up the entire basic process and working of the service, the user specifies the target, condition (logic or any condition when the alert should trigger) and action group. Azure monitors the provided target and when the specified conditions are met an alert is triggered and sent to the action group.
Impact
When the security policy alerts are not created and enabled the organization will miss out the alerts regarding the updates in any of their security policies.
Consider a scenario in an organization where the security team has created some security policies, rules defined for specific security conditions that need to be controlled. Now, under some circumstances, intentionally or unintentionally, these security policies are altered but not in favour of the company and if the alert rule for ‘update security policy’ is not created the loophole might remain unnoticed for a long period of time and/or suffer attacks causing instability in the organization.
Steps to Reproduce
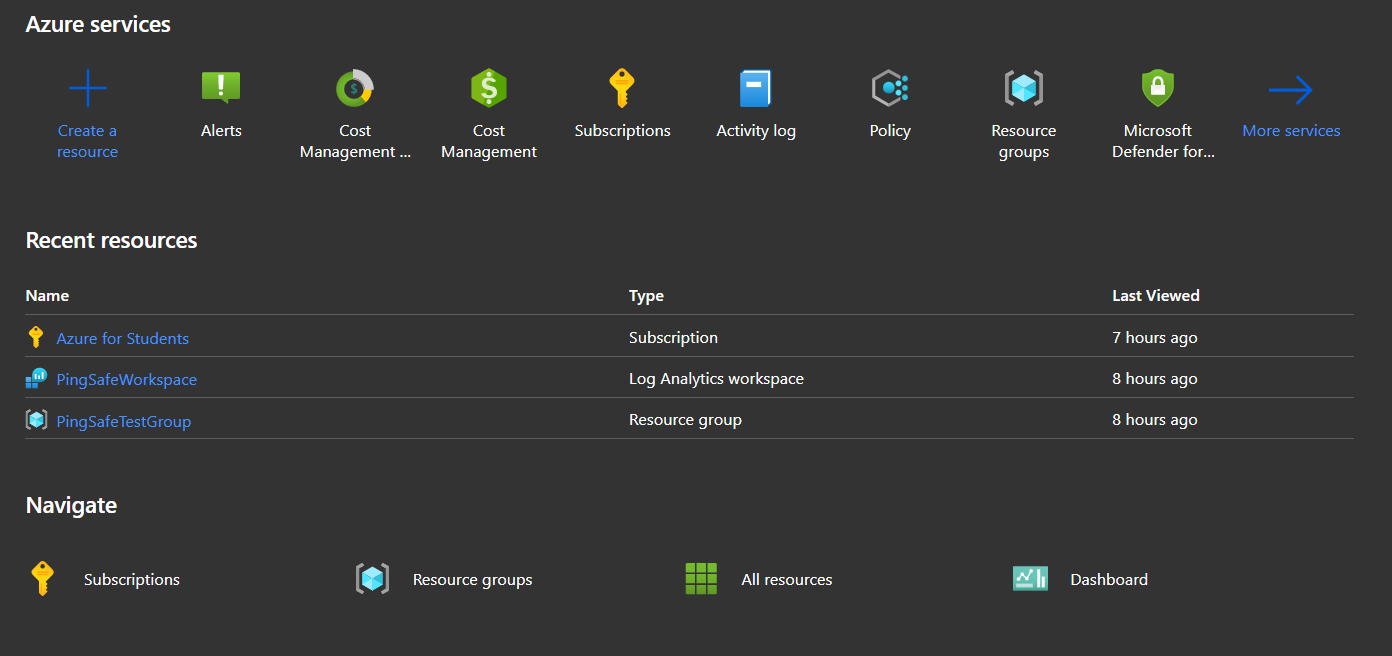
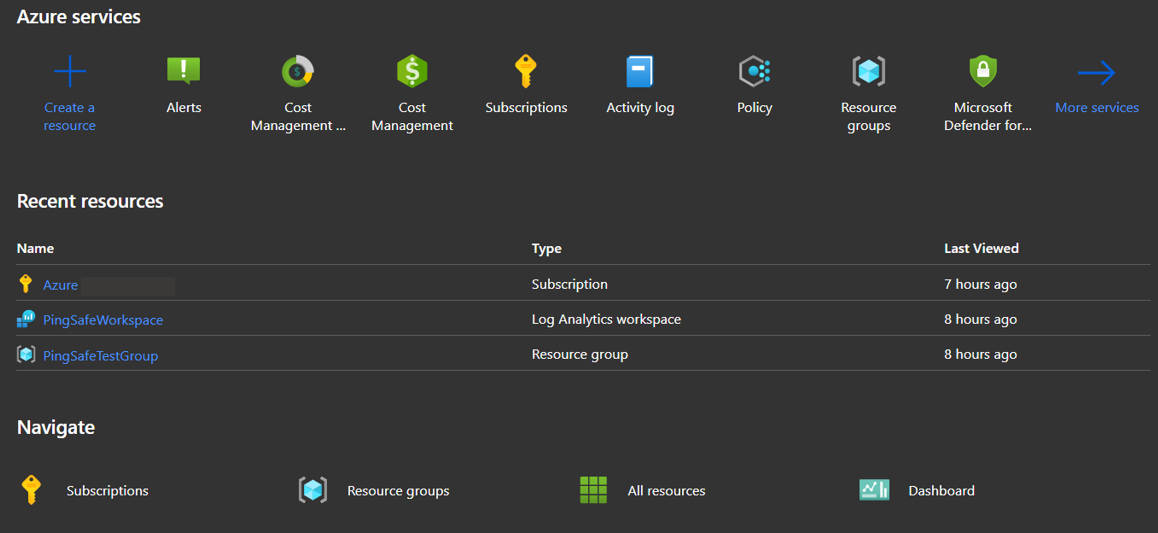
- Login to the Azure account.
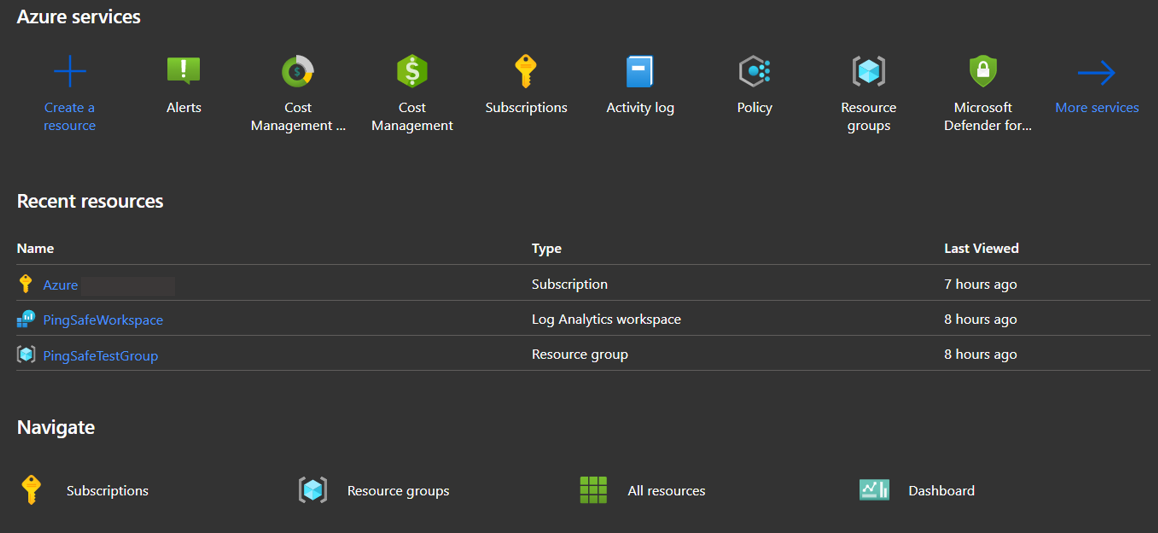
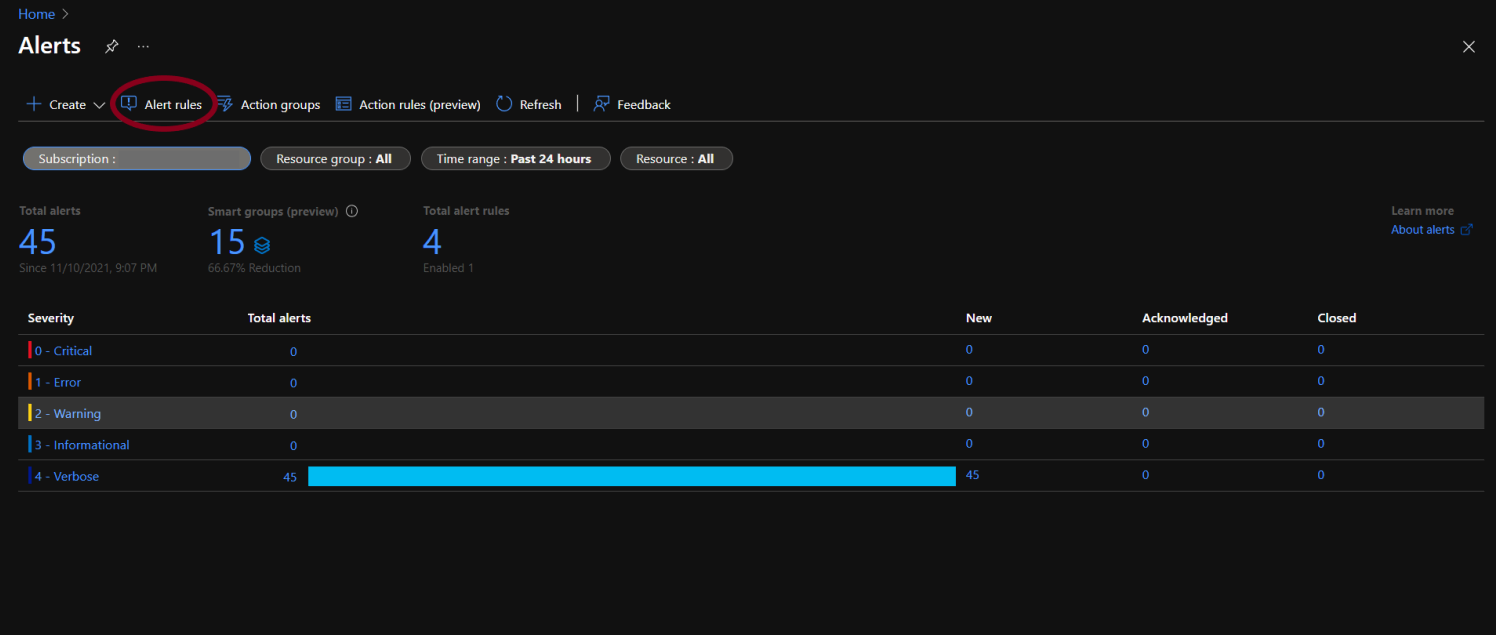
- From Azure services, select Alerts.
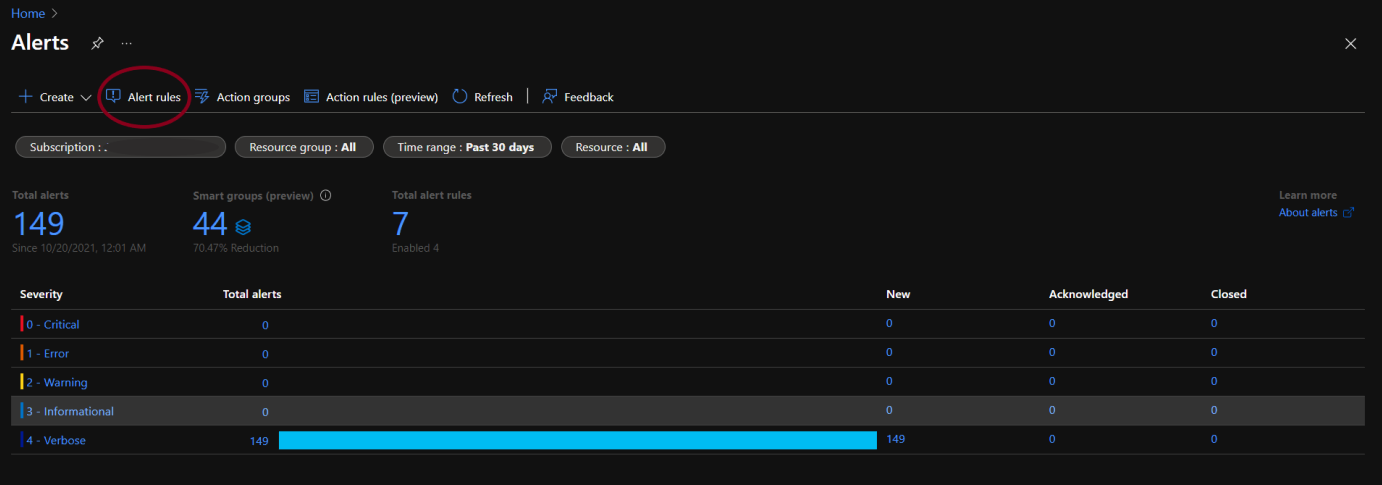
- The Alerts page will open, select the Alert rules option.
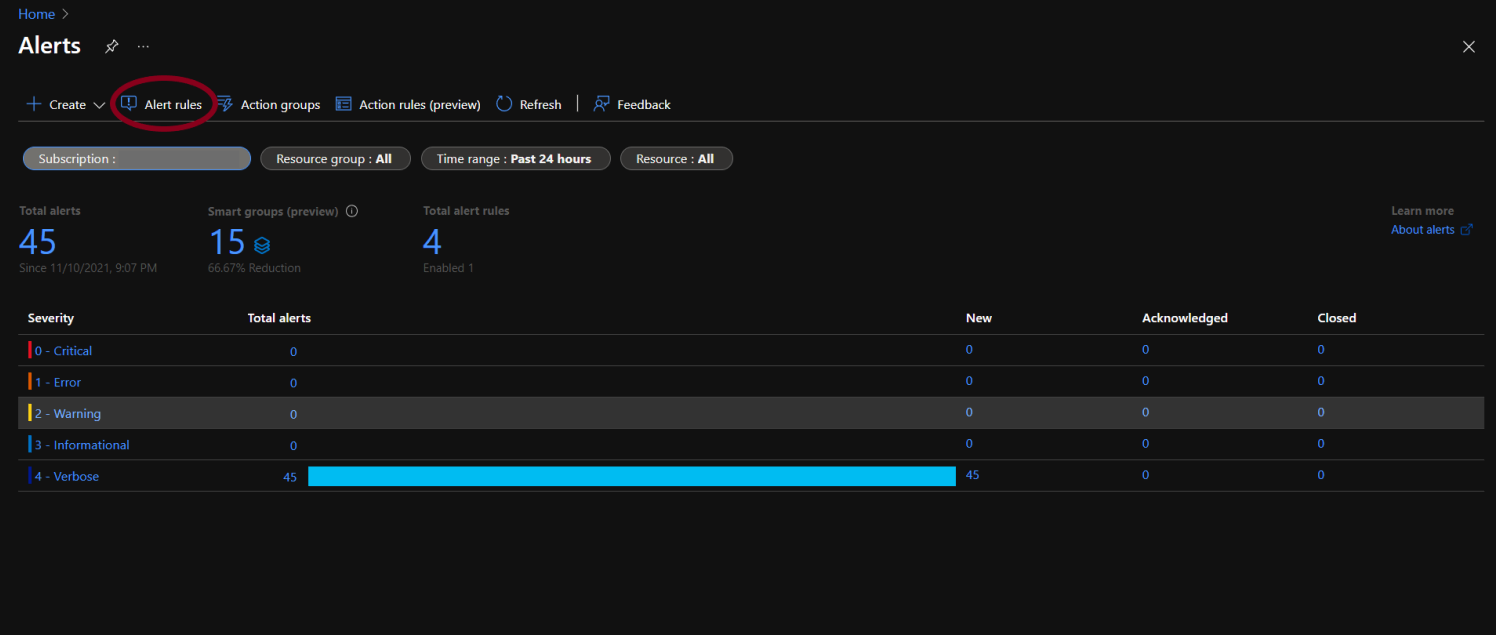
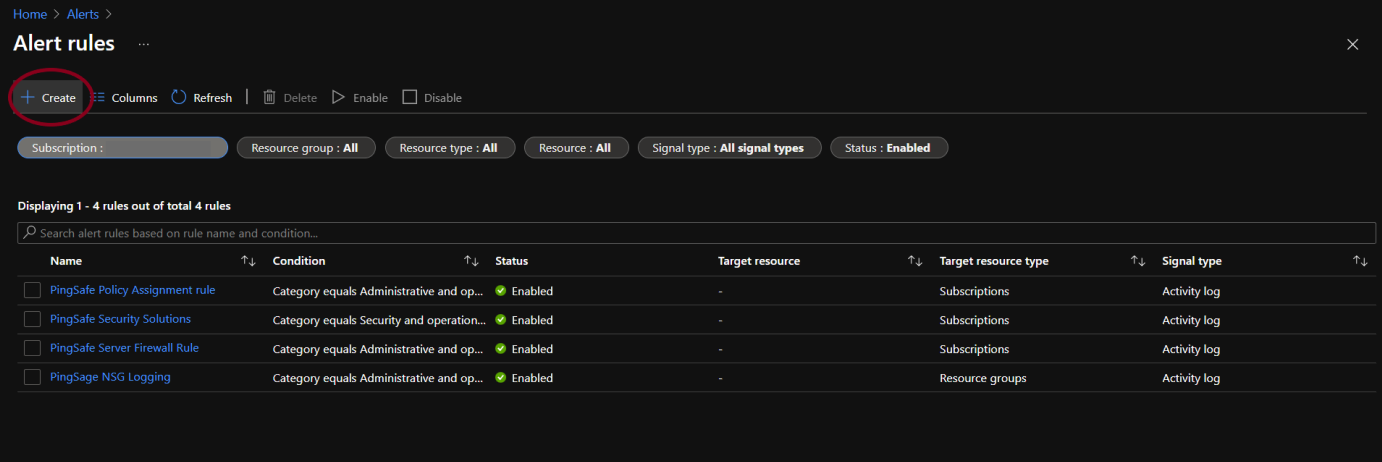
- The alerts rule page will appear. By default, only the enabled alert rules are shown on the screen.
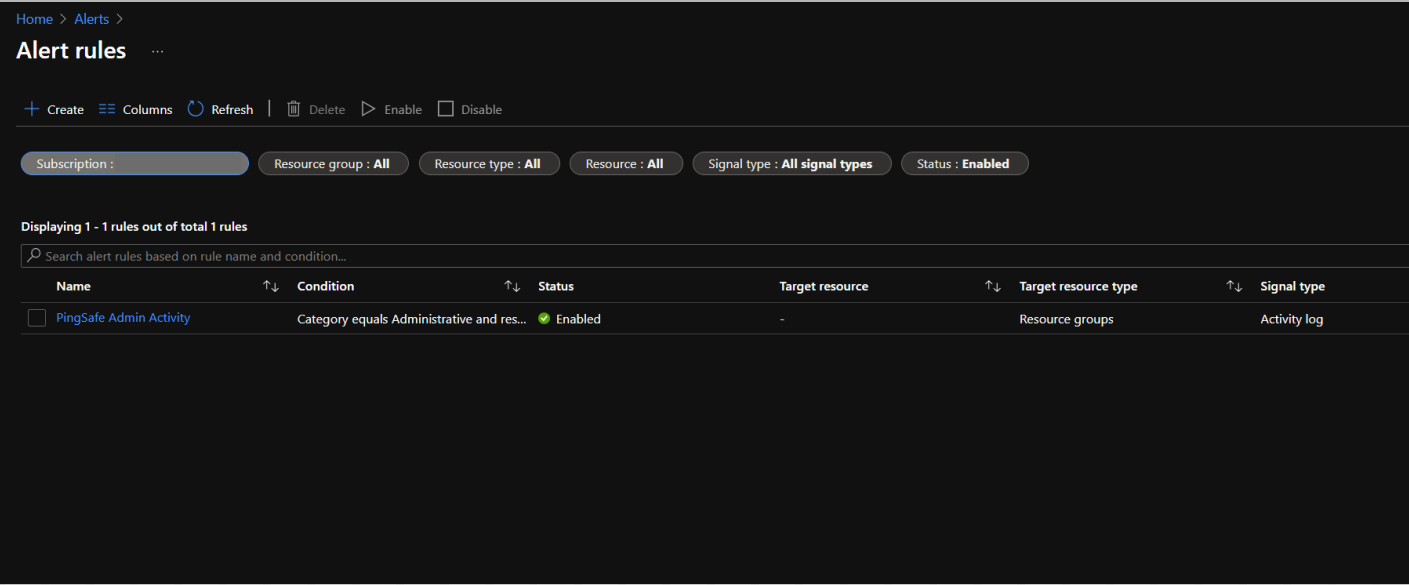
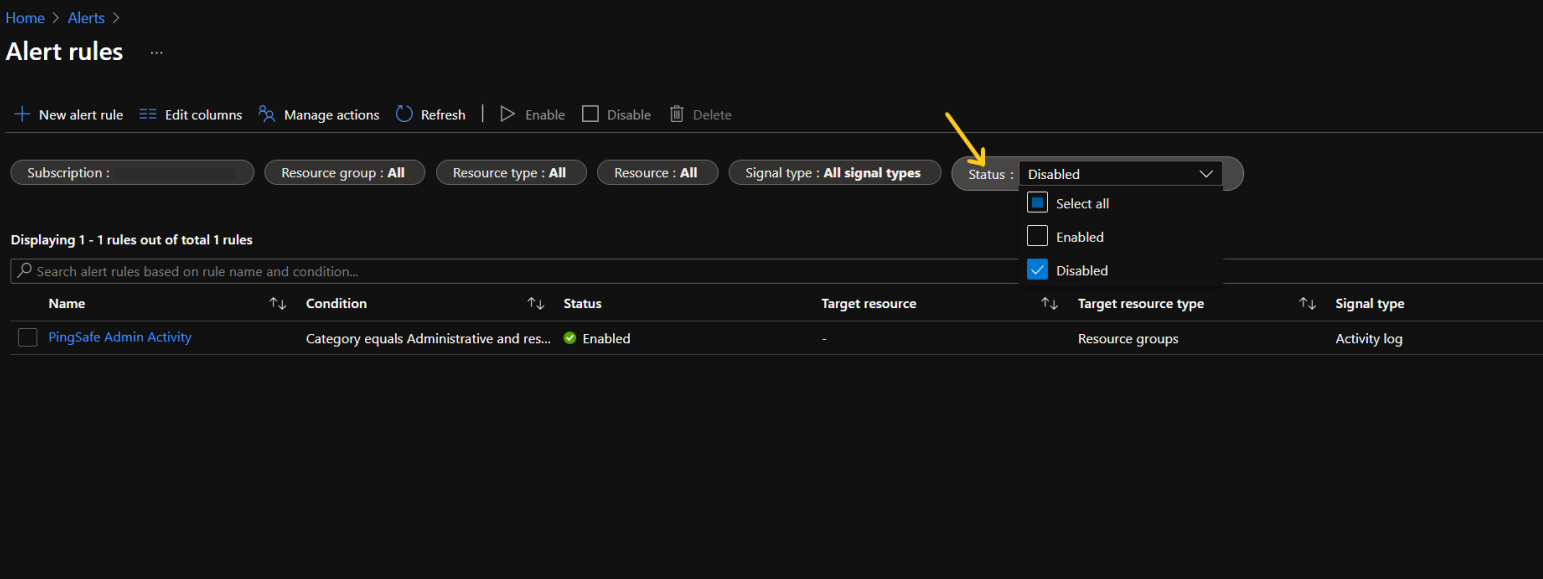
- To check the list of disabled alert rules as well, go to the Status option and click on Select all.
- Now we will check for 2 things:
- Whether the security policy update rule is created.
- If the security policy alert is created then is it enabled.
- Search alert rules based on rule name:
- If the user remembers the security policy alert rule name, simply type it in the search bar given above the list of subscriptions.
- Now check the status of the alert rule and check the Status. If the Status is set as Disabled, we need to enable it. To do so follow from steps under the Steps for Remediation section given next to the current section(Steps to reproduce).
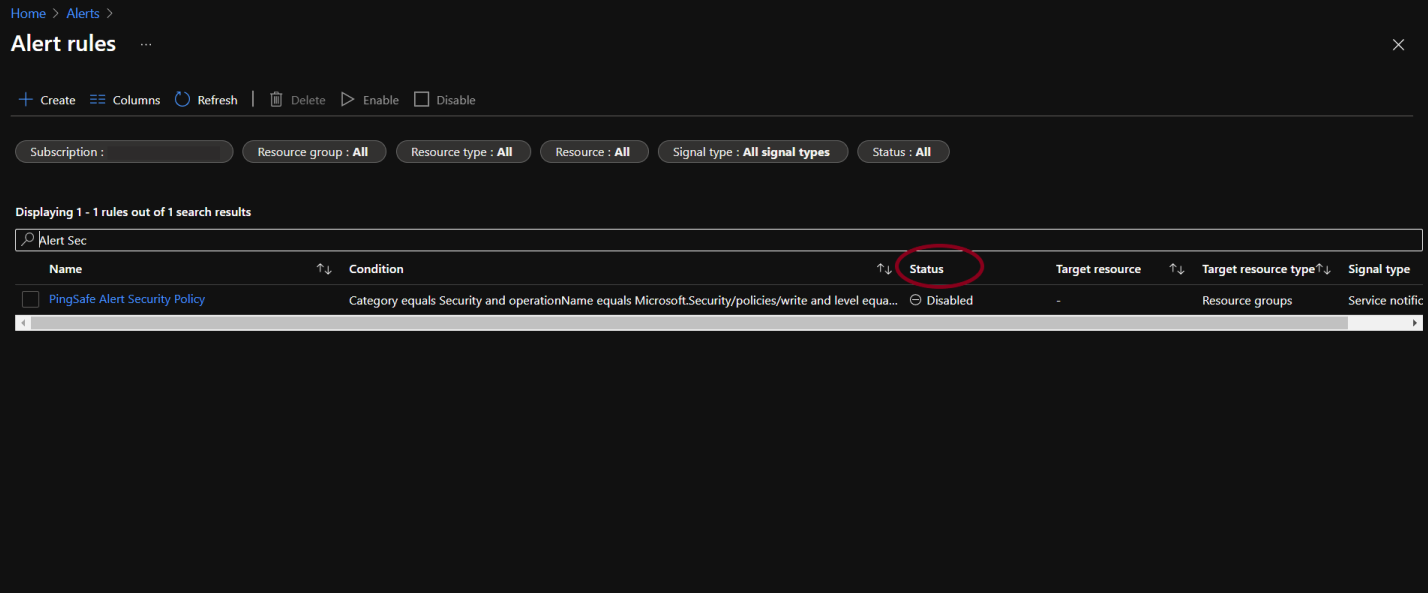
- If the user remembers the security policy alert rule name, simply type it in the search bar given above the list of subscriptions.
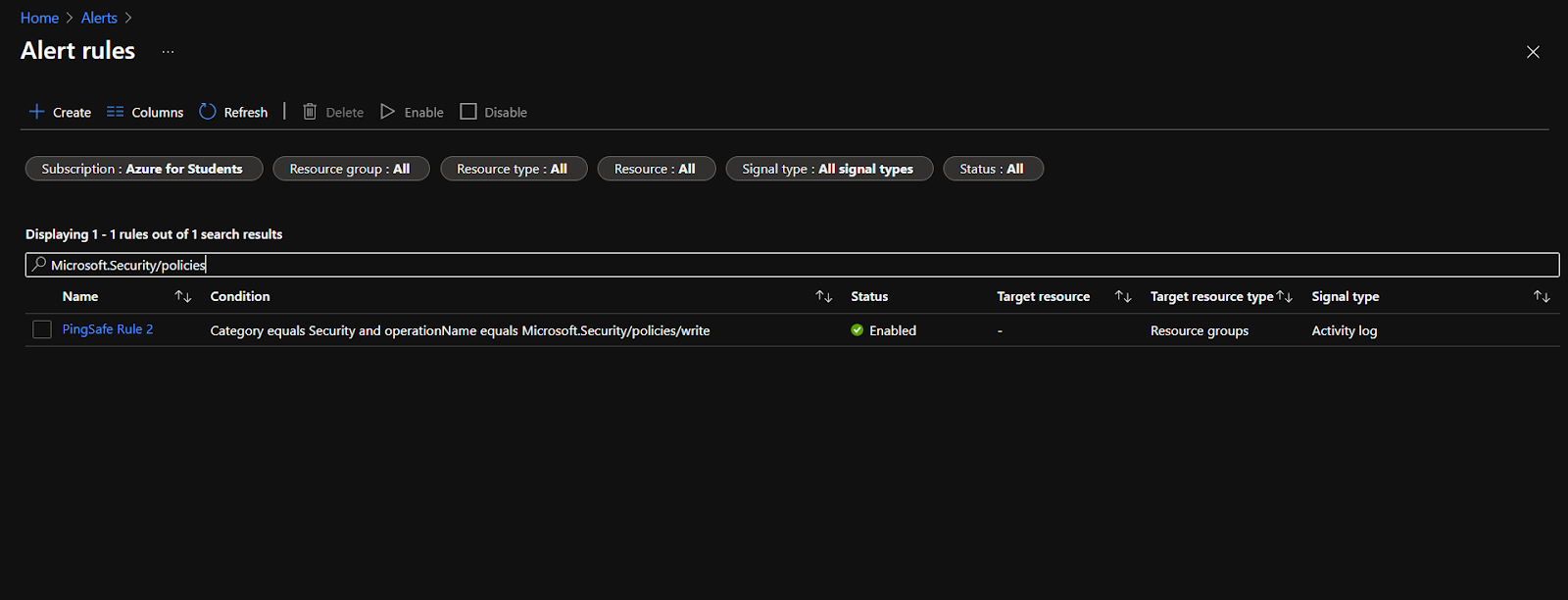
- Search alert rules based on condition:
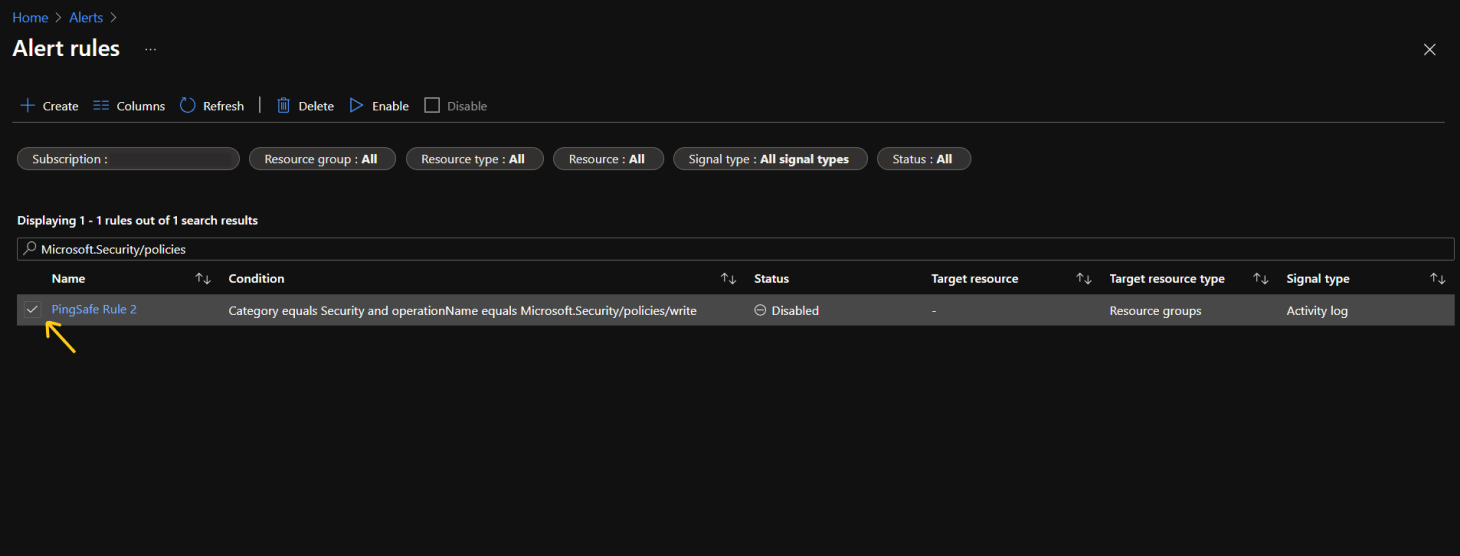
- In case the rule name is not known, in the search bar type ‘Microsoft.Security/policies’.
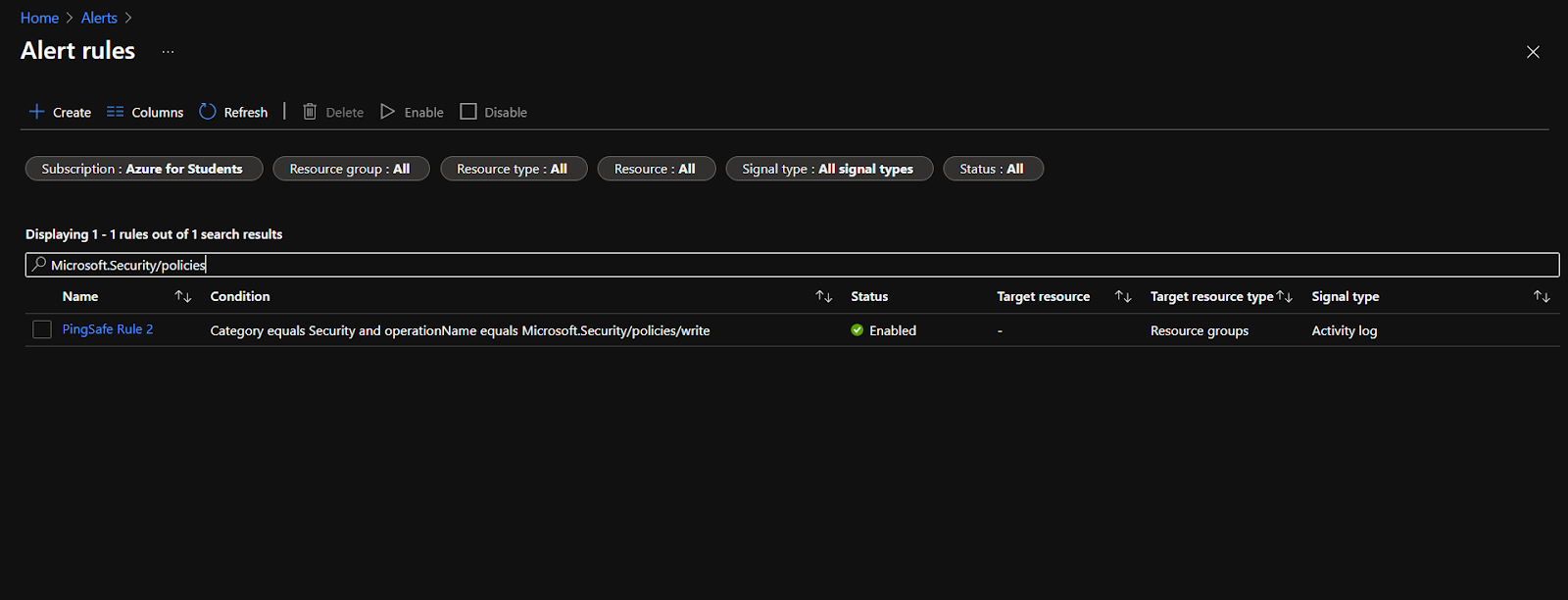
- In case the rule name is not known, in the search bar type ‘Microsoft.Security/policies’.
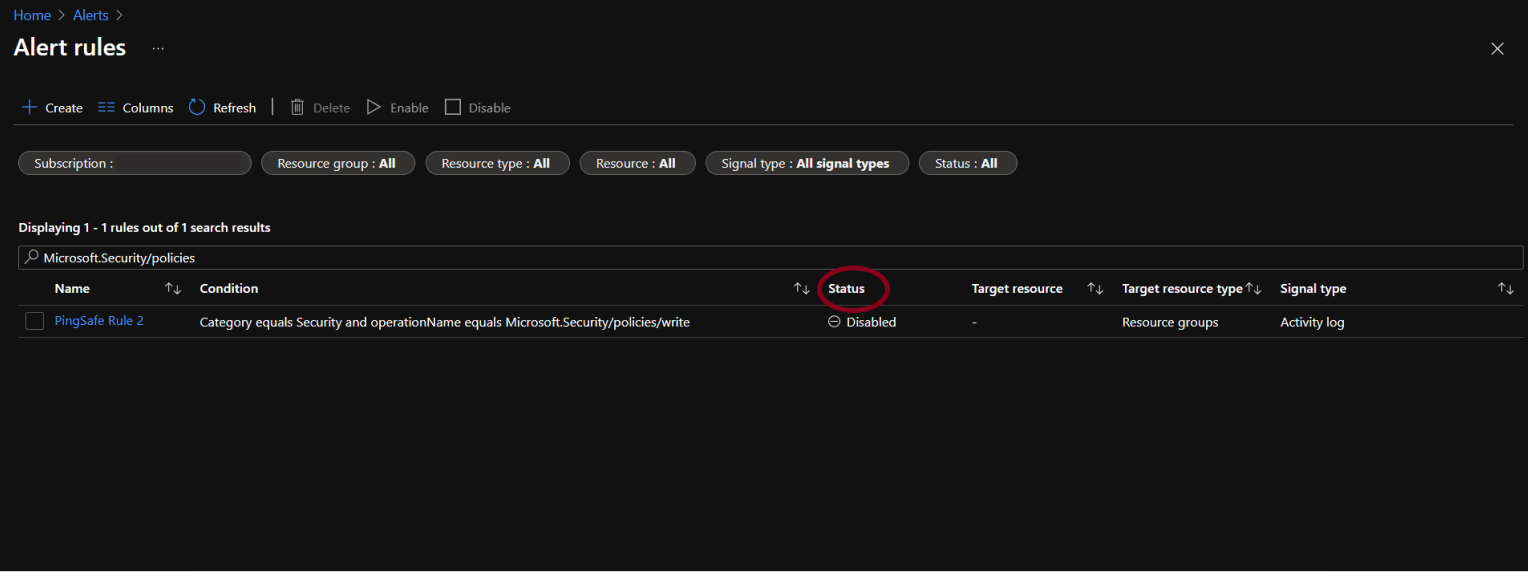
- If the status is set as Disabled then go to Enable Alert Rule under Steps for Remediation section and follow the steps.
- Else, if the screen appears blank, we will have to create a security policy rule first. To check the steps of creating a security policy rule, click here.
Steps for Remediation
Create Alert Rule:
- Login to the Azure account.
- From Azure services, select Alerts.
- The Alerts page will open. Click on Alert rules.
- Click on +Create.
- Select the target resource by clicking on the Select Resource option.
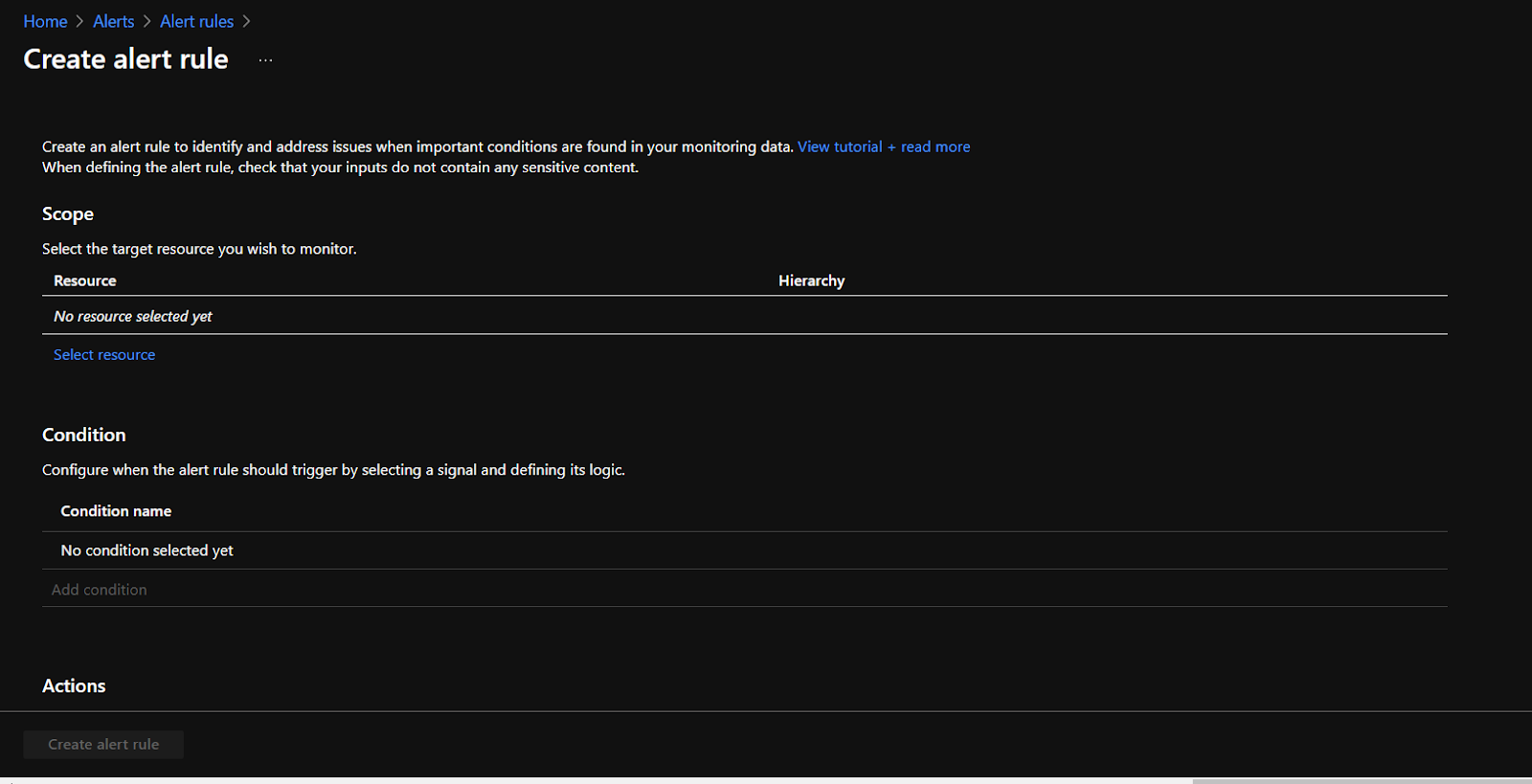
- Under the Conditions section, click on Add condition.
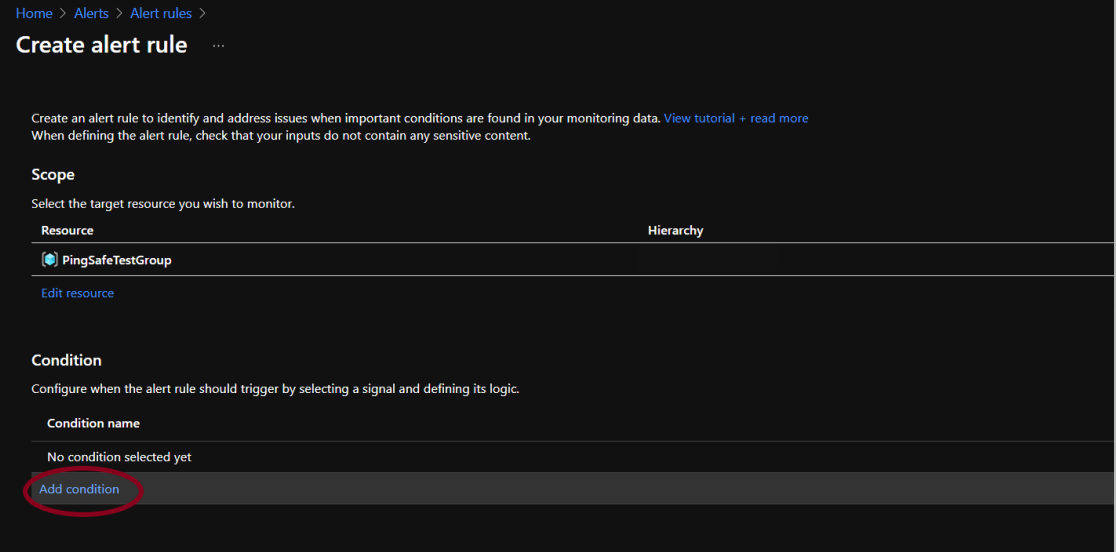
- Click on the search bar and type “Policy Assignment”, select the signal “Update security policy (Microsoft.Security/policies)”. Click on Done.
- Users can then select an action group(optional). Next, provide the alert rule name as desired and give a little description to it for later reference (optional).
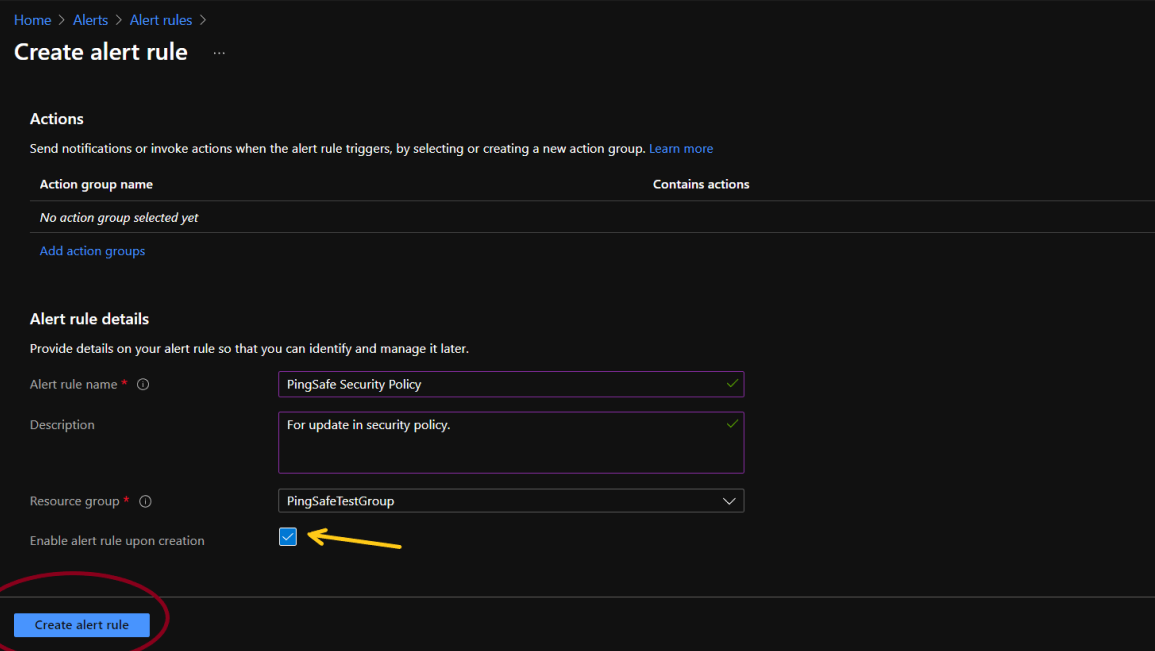
- By default, the alert rule is enabled but it is recommended to cross verify it and then click on Create alert rule.
Enable Alert Rule:
- Login to the Azure account.
- From Azure services, select Alerts.
- The Alerts page will open. Click on alert rules.
- To check the list of disabled alert rules as well, go to the Status option and click on Select all.
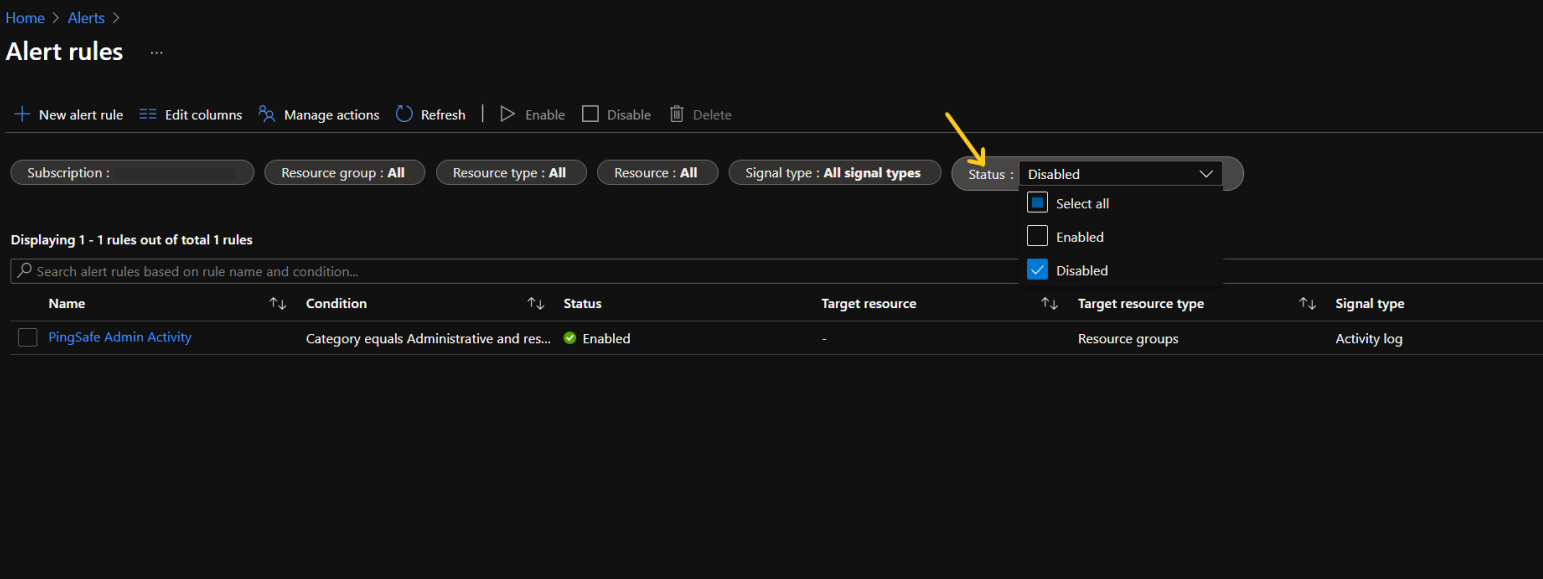
- To search alert rules based on:
- Rule name: Type the rule name in the search bar.
- Rule condition: In the search bar write, “Microsoft.Security/policies”.
- Rule name: Type the rule name in the search bar.
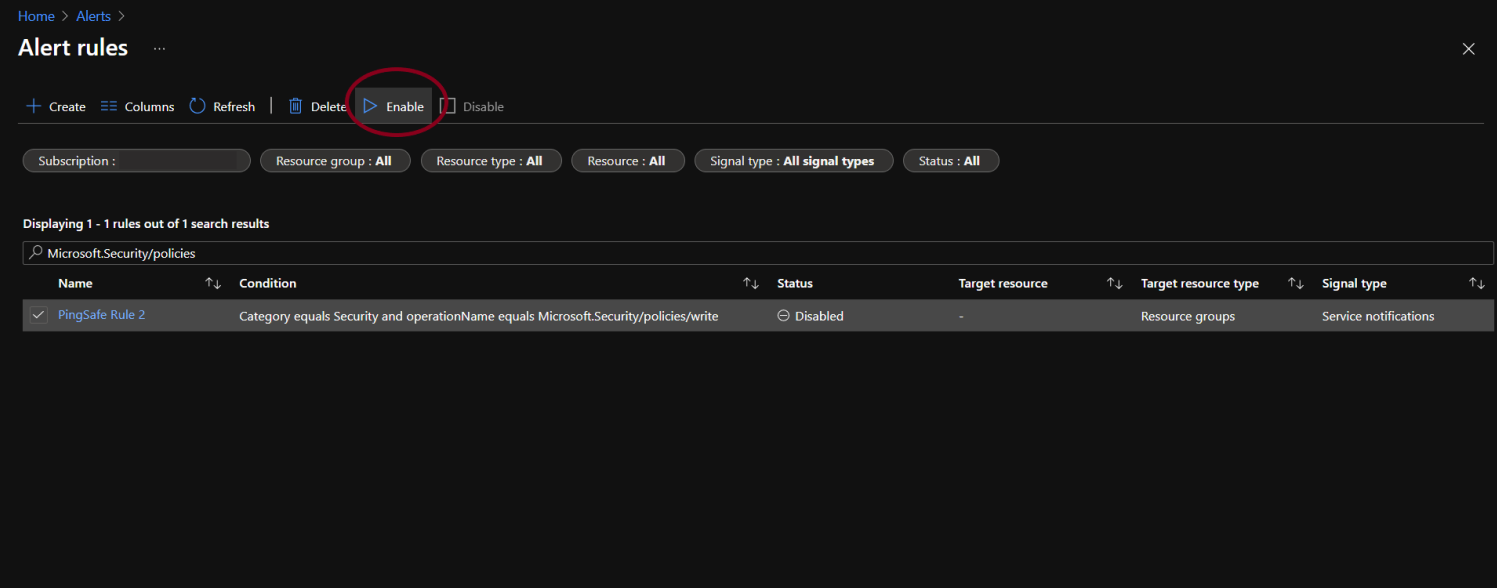
- The required alert rule(s) will appear on the screen. Click on the check-box of the concerning alert rule(s).
- Click on Enable and wait for a few minutes for the changes to get reflected.
Please feel free to reach out to support@pingsafe.ai with any questions that you may have.
Thanks
PingSafe Support