Elastic Block Store Unencrypted Volumes
This plugin ensures Elastic Block Store volumes are encrypted at rest.
Risk Level: Medium
Description
This plugin ensures Elastic Block Store volumes are encrypted at rest. Elastic Block Store volumes must be encrypted with an AWS KMS key to ensure that data is not exposed in case of a data breach.
About the Service
Amazon EC2: Amazon Elastic Compute Cloud (Amazon EC2) provides scalable computing capacity in the Amazon Web Services (AWS) Cloud. With the EC2 instance, you can launch as many virtual servers as you need, configure security and networking, and manage storage without worrying about the hardware needs of the process. Security Groups act as a firewall for an EC2 instance to control the incoming and outgoing traffic. You can read more about security groups here.
Impact
EBS volumes can contain critical information of the running EC2 instances. If exposed to the public, anyone over the Internet can have access to it. Therefore, it must be encrypted before storing data to avoid data readability.
Steps to Reproduce
Using AWS Console-
- Log In to your AWS Console.
- Open the EC2 Management Console. You can use this link (https://console.aws.amazon.com/ec2) to navigate directly if already logged in.
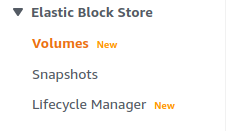
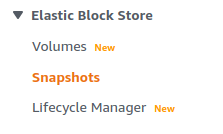
- Move to the Volumes in the Elastic Block Store section from the left navigation pane.
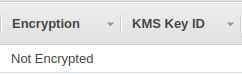
- A list of volumes available will be displayed. Check the Encryption column, if it is equal to “Not Encrypted”, the vulnerability exists.
- Repeat steps for all the EBS volumes you want to investigate.
Steps for Remediation
Configure volume encryption and delete unencrypted Elastic Block Store snapshots.:
- Log In to your AWS Console.
- Open the EC2 Management Console. You can use this link (https://console.aws.amazon.com/ec2) to navigate directly if already logged in.
- Move to the Volumes in the Elastic Block Store section from the left navigation pane.
- A list of volumes available will be displayed. Select the vulnerable volume by clicking on the check box next to it.
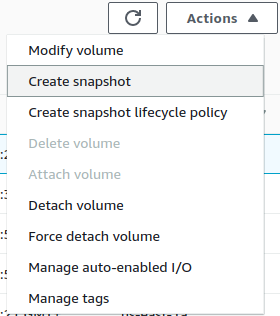
- From the Actions menu drop-down box, click on Create Snapshot.
- A new snapshot will be created for the volume. Move to the Snapshots section now.
- From the list of snapshots available, select the newly created snapshot by clicking on the checkbox next to it.
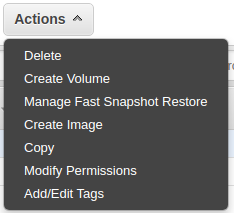
- From the Actions drop-down menu, click on Create Volume.
- Check the Encryption option to enable encryption of the volume, and select the AWS KMS key that will be used for encryption.
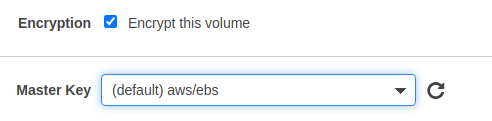
- Click on Create Volume to create a secure encrypted volume.
- Now, again move to the Volumes section and select the original vulnerable volume.
- From the Actions drop-down menu, click on Delete.
- If the Delete option is greyed out, first Detach the instance and then Delete the EBS volume.
- Repeat steps for all the vulnerable EBS volume.