Open CIFS
Risk Level: High
Description:
This plugin determines if UDP port 445 for CIFS is open to the public. Also, it consists of valid steps or measures to be taken to avoid unhealthy vulnerability to all IP addresses ranges i.e. 0.0.0.0/0. While some ports such as HTTP and HTTPS are required to be open to the public to function properly, more sensitive services should be restricted to known IP addresses.
About the Service :
DigitalOcean Firewall:
DigitalOcean Cloud Firewalls are an organization-based, stateful firewall administration for Droplets given at no extra expense. Cloud firewalls block all traffic that isn't explicitly allowed by a standard. Firewalls place an obstruction between your servers and different machines in the organization to safeguard them from outer assaults. Firewalls can behave based, which are designed on a for every waiter premise utilizing administrations like IPTables or UFW. Others, such as DigitalOcean Cloud Firewalls, are network-based and stop traffic at the organization layer before it arrives at the server.
Impact :
Firewalls for the droplets are used to control the incoming and outgoing traffic. There are rules defined under firewalls that can allow specific IP addresses to access the droplets with the protocol and the Ports specified. Allowing CIFS access can result in increased opportunities for malicious activity such as Denial of Service (DoS) attacks, man-in-the-middle attacks (MITM), or the Windows Null Session Exploit.
Steps to Reproduce :
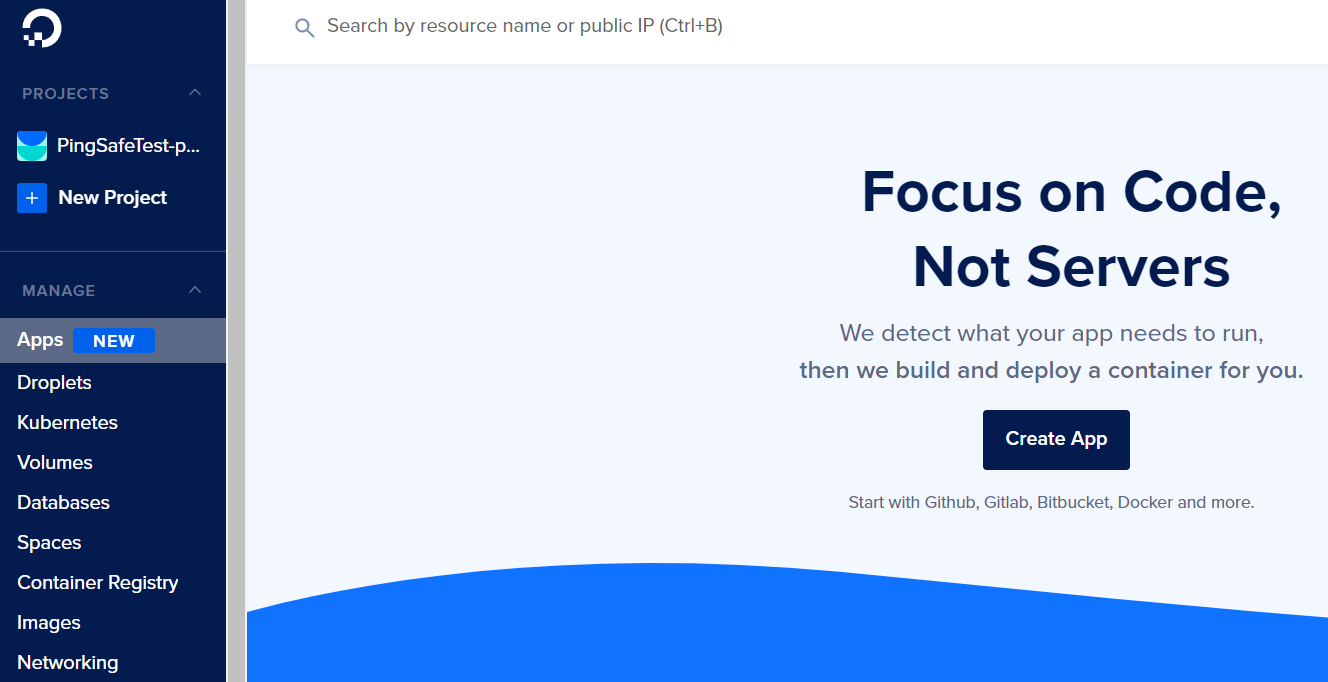
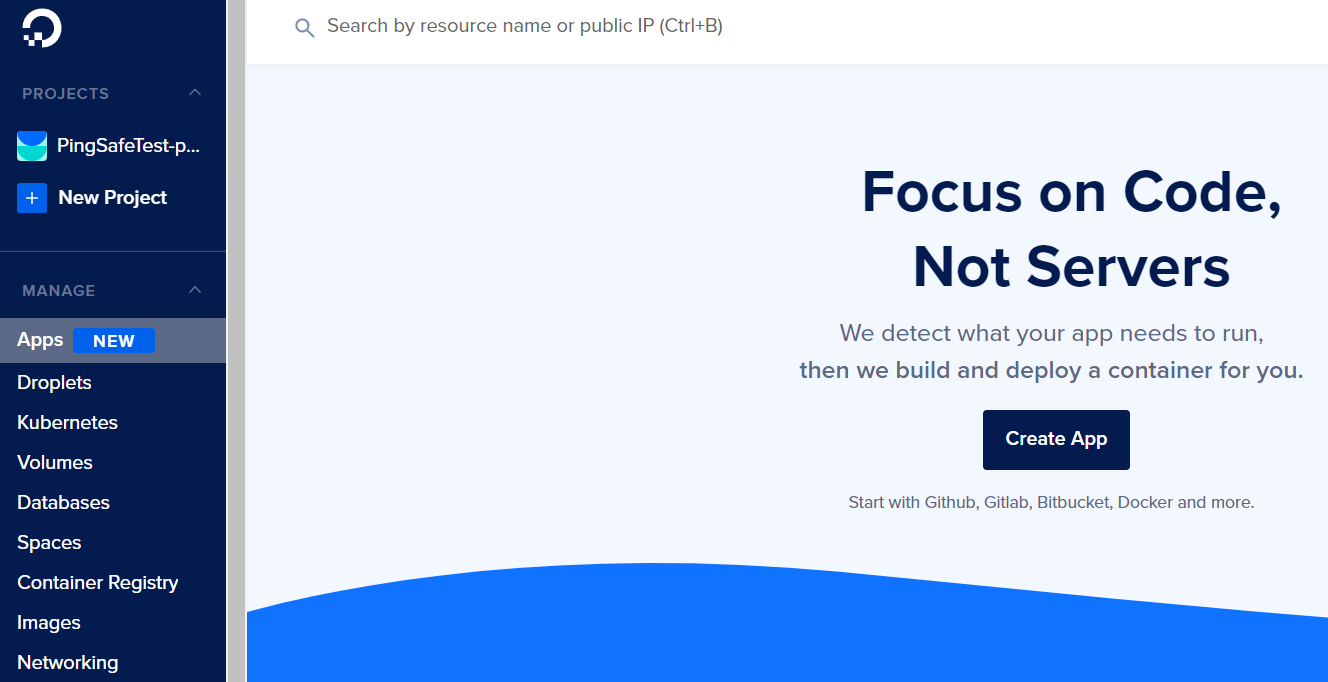
- Login to the digital ocean console.
- Select Networking under the MANAGE section.
- Switch to the Firewalls tab.
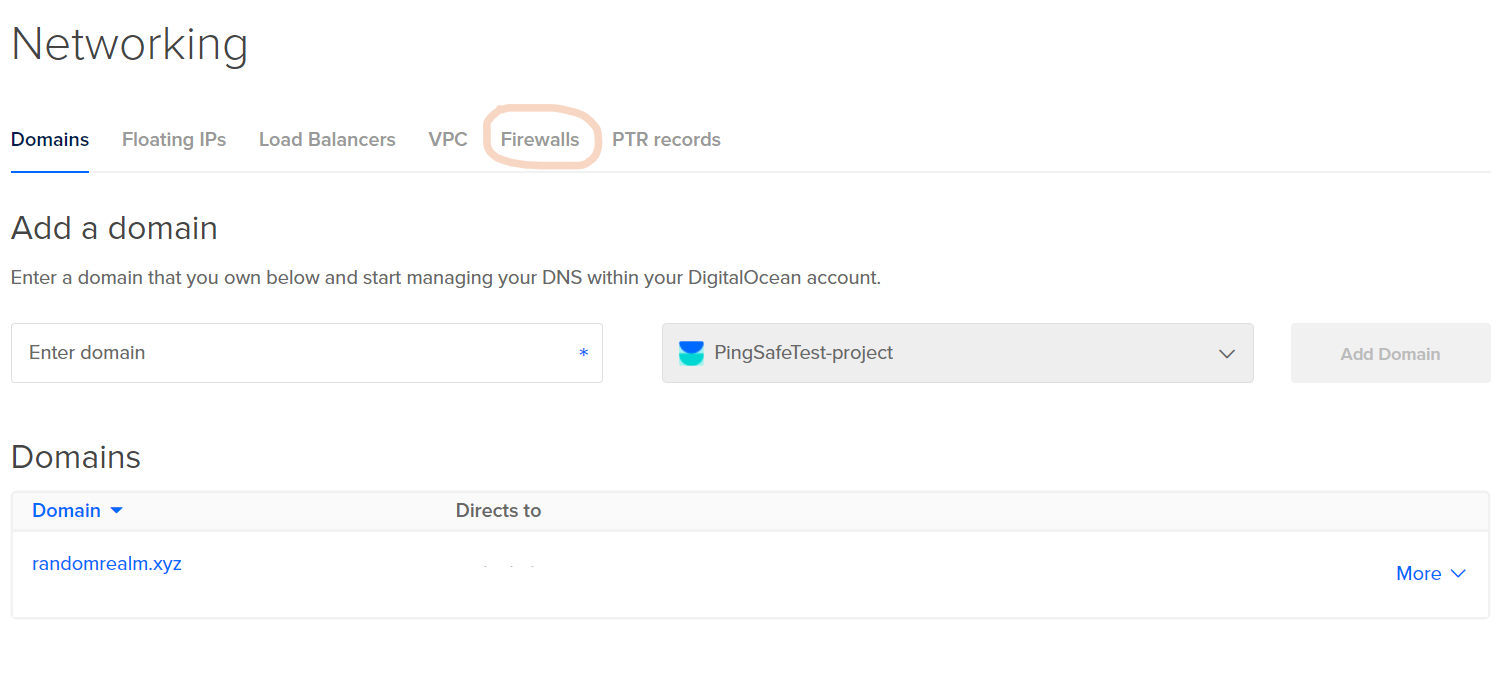
- Select a firewall from the given lists.

- Check under Inbound Rules and/or Outbound Rules, if the Type is set to All UDP/custom, Protocol as UDP and Port Range includes either All ports or port 445, visit the Steps for Remediation section.

- Repeat the process for other firewalls as well.
Steps for Remediation :
- Login to the digital ocean console.
- Select Networking under the MANAGE section.
- Switch to the Firewalls tab.
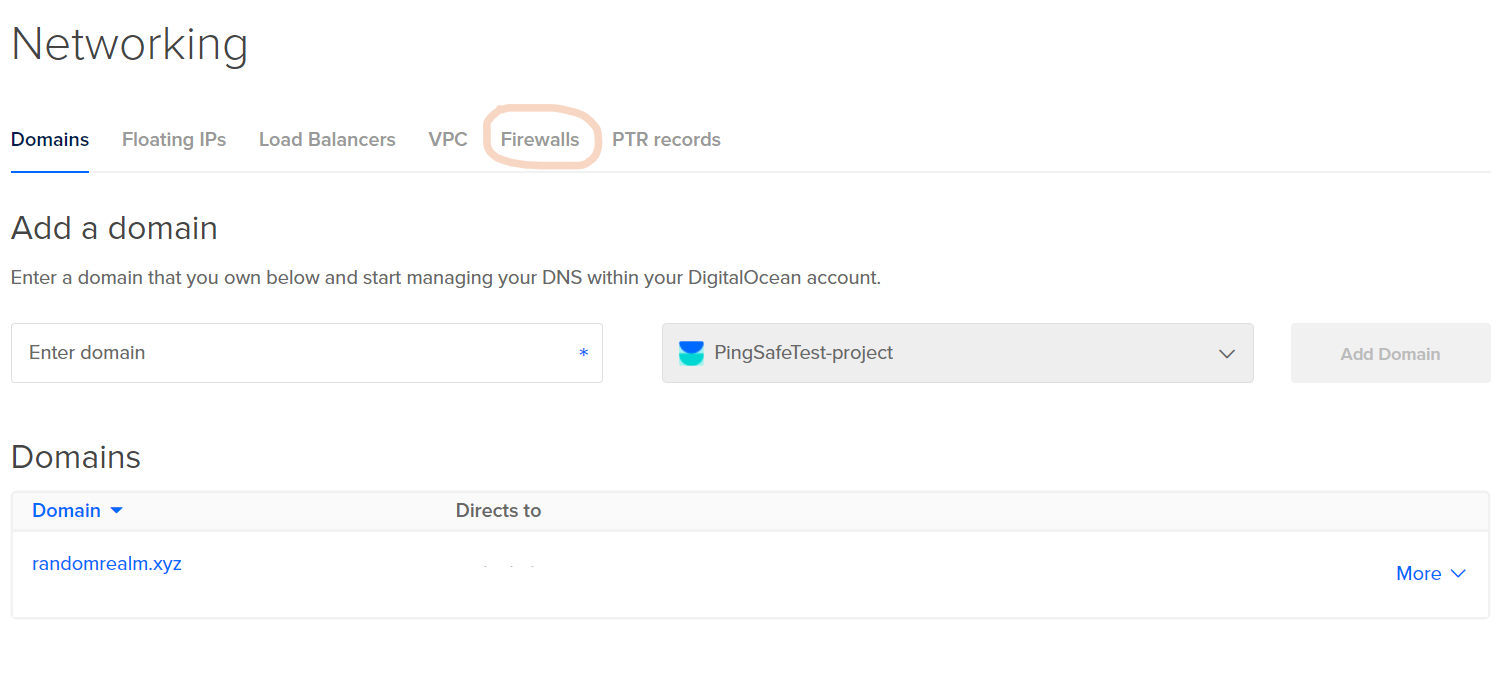
- Select a firewall from the given lists.

- Check under Inbound Rules and/or Outbound Rules, if the Type is set to All UDP/custom, Protocol as UDP and Port Range includes either All ports or port 445, we will have to change the source and destination for the port to enhance security.

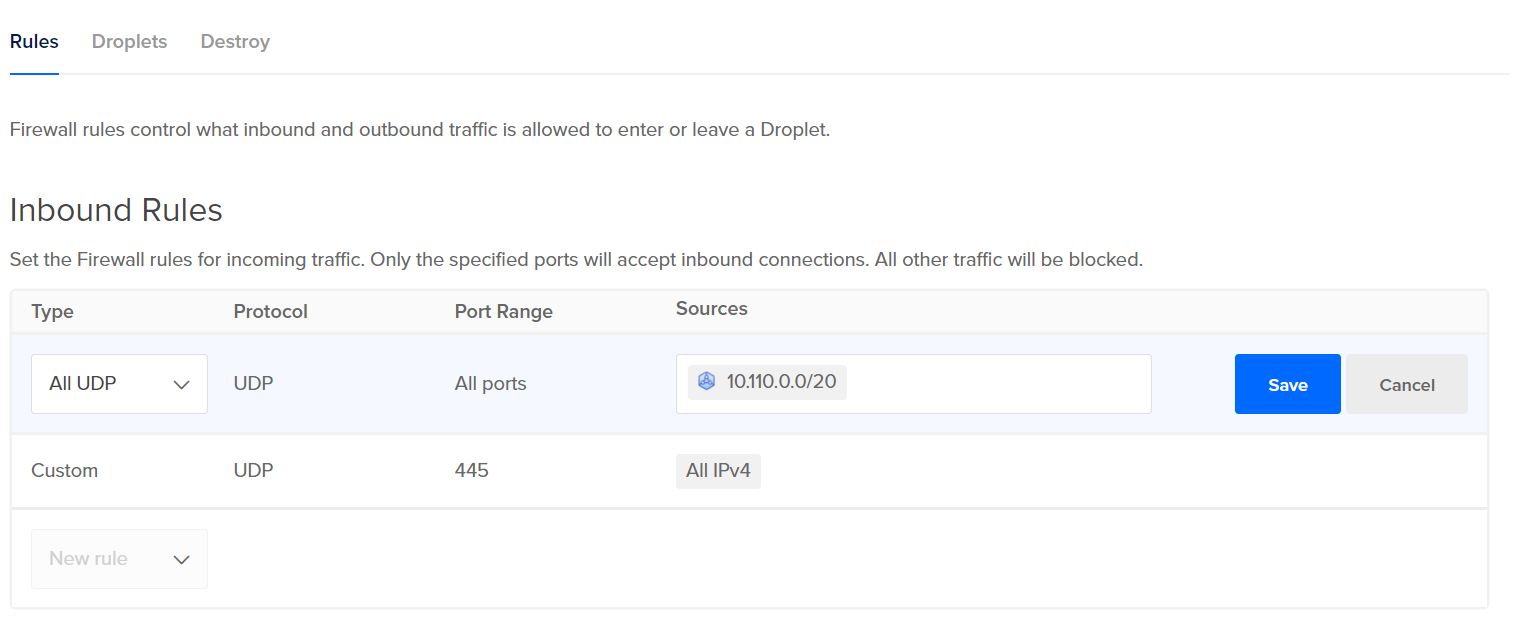
- Select the rule in which port 443 is open to all source or destination by clicking on More, click on Edit Rule.
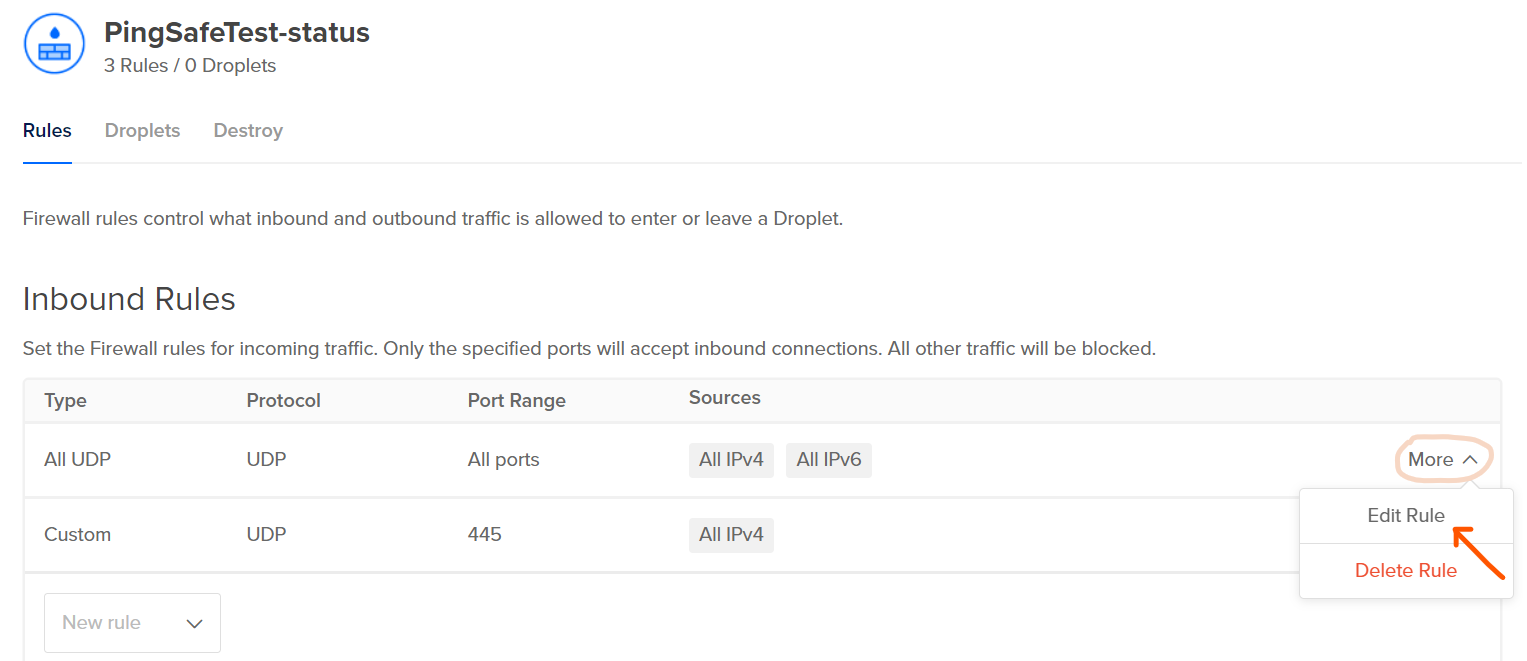
- Under Sources remove All IPv4 and All IPv6 options, add the eligible source (in Inbound Rules) / destination (in Outbound Rules) IP address and click on Save.
- Repeat the process for other firewalls as well.